Amrisha Prashar
on 3 May 2016
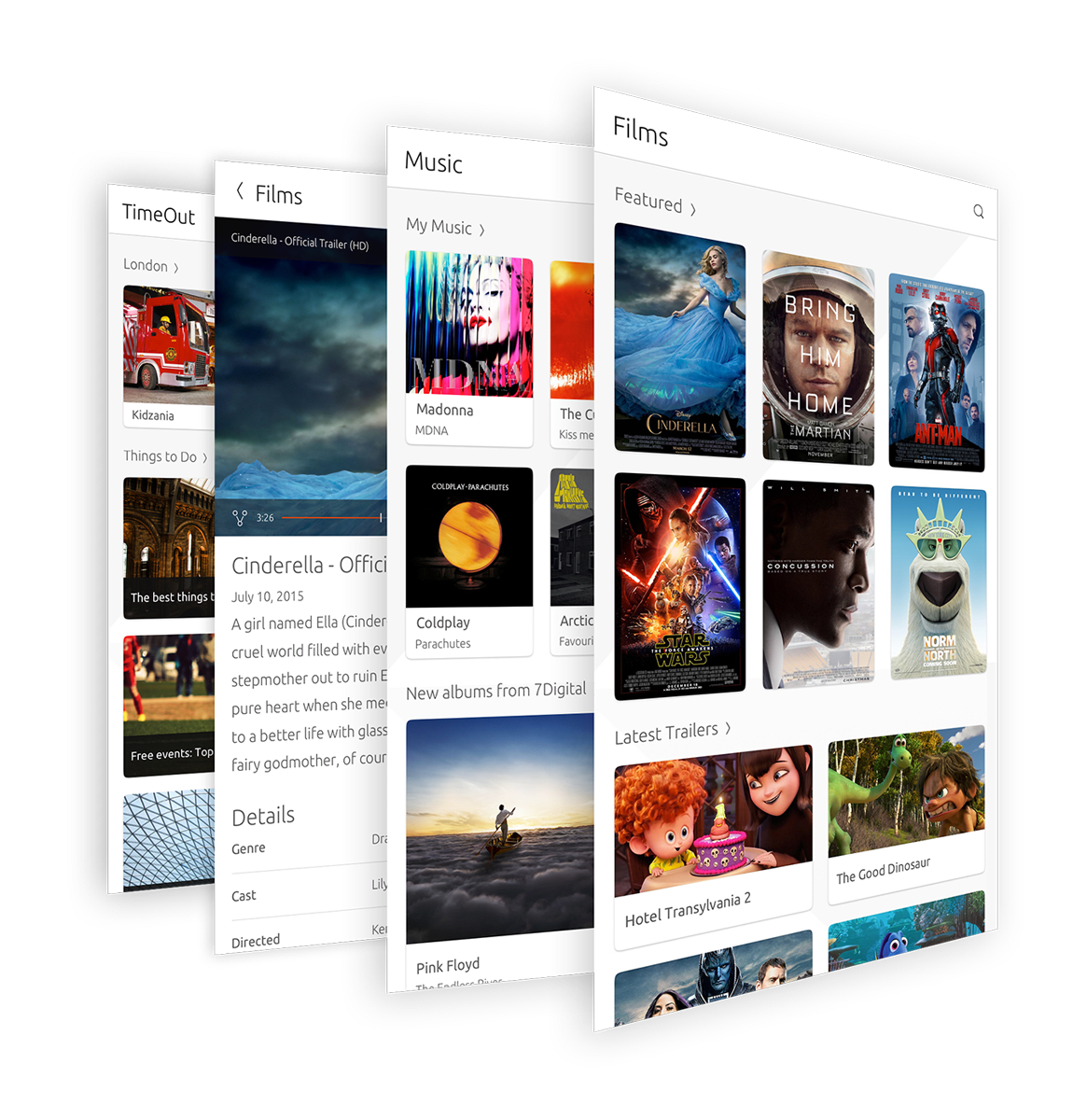
We’ve come along way on the Scopes journey. We first launched them over a year ago to show you a new way to enjoy content and services on your smartphones without relying on traditional apps. Scopes bring everything you need onto one screen without the need to open and switch between multiple apps – revolving around the content and services that matter to you.
With one year on Scopes have evolved much more to show more personal information (by adding a relevant account in settings), better interactions (e.g. viewing comments, posting, liking, subscribing) and search filtering.
For a complete list of the Scopes that have changed view / download the table below!



